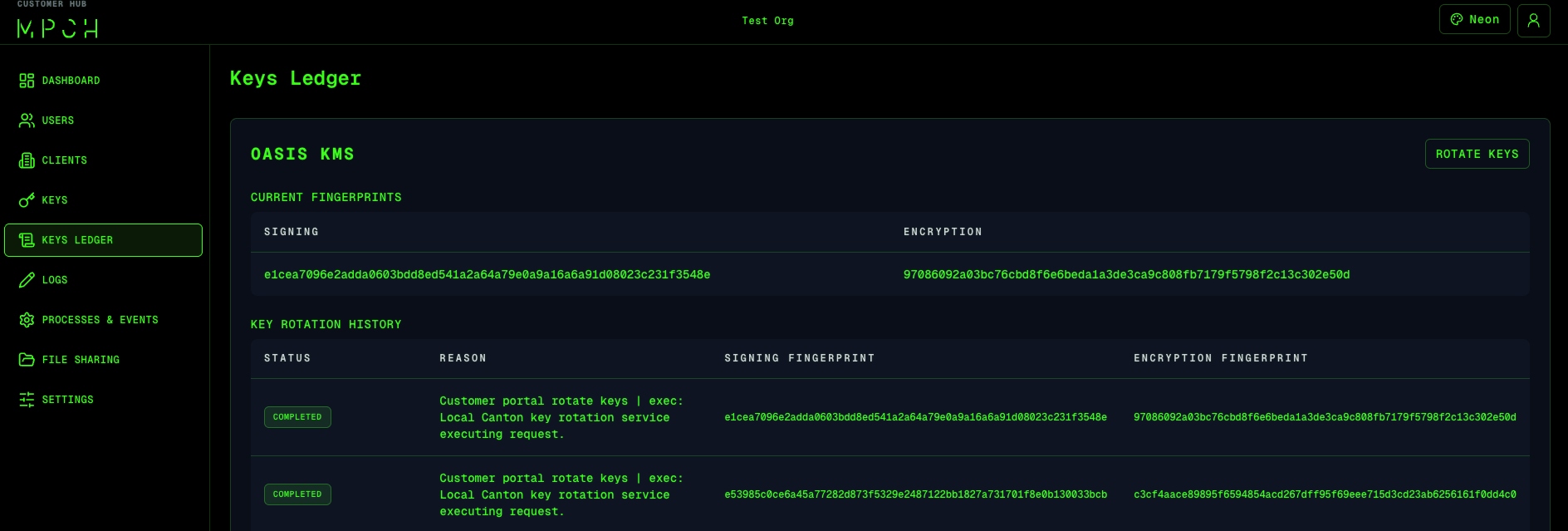
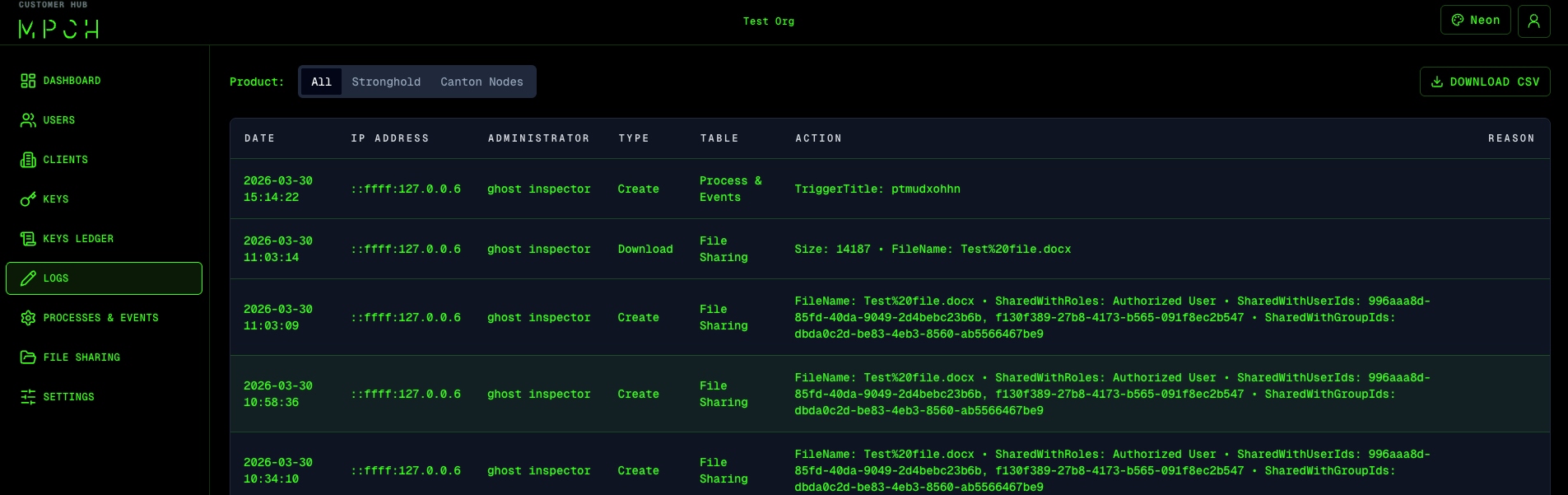
System-Level Keys
Wallet keys move assets. System-level keys protect the network itself. In Canton, security isn't just about asset custody — it's about trust in every node, every transaction, and every rule embedded in the system. System-level keys power encrypted state sharing, consensus, and operational logic. And these same patterns apply across any infrastructure where authority keys govern trust.